Google rolled out a new reCAPTCHA flow this week. If a site decides you look suspicious, it stops asking you to identify crosswalks and starts asking you to scan a QR code with an "approved" iOS or Android device — one that can pass Google's Play Integrity API or Apple's App Attest.
No approved phone, no entry.
The GrapheneOS project flagged it within hours. The Hacker News thread — titled “Hardware Attestation as Monopoly Enabler” — hit nineteen hundred points and six hundred comments overnight. Cybernews, Digital Trends, CyberInsider, and Cointelegraph all picked it up by morning. Privacy advocates are calling it what it is: the moment the open web started checking ID at the door.
WHAT ACTUALLY CHANGED
The old reCAPTCHA was a behavioral puzzle. It looked at your mouse jitter, your browser fingerprint, your traffic patterns, and a thousand other signals to guess whether you were a human. It was creepy, it was Google, and it mostly worked.
The new flow — reCAPTCHA Mobile Verification — is something different. When the system isn’t sure about you, it asks you to prove yourself by handing the puzzle off to a phone that Google or Apple has cryptographically signed off on. Your phone’s secure element generates an attestation, signed by hardware keys baked in at the factory, proving the device is running an OS that the manufacturer and Google approve of. The server checks the signature. If it verifies, you’re in. If it doesn’t, you’re a bot.
That word — “approved” — is the entire story.
WHO GETS APPROVED
Google's Play Integrity API is the gatekeeper on the Android side. It hands out three integrity levels — BASIC, DEVICE, and STRONG — and a phone passes only if it boots a Google-certified OS, with a locked bootloader, on hardware that holds a Google-issued attestation key. STRONG integrity, which sites can demand at will, requires hardware-backed attestation from the device's secure element.
Here's the part that should make every privacy-conscious reader sit up: Play Integrity will happily approve a stock Android phone that hasn't seen a security patch in ten years. It will not approve GrapheneOS — the open-source, hardened, audited Android fork that the GrapheneOS team and most serious security researchers consider the most secure consumer phone on the planet.
Let that sit for a second. A decade-old, unpatched Galaxy running spyware from six manufacturers passes. A Pixel running GrapheneOS — the OS Edward Snowden recommends, the OS Motorola just partnered with for enterprise security, the OS that blocked three Cellebrite zero-days last year — fails.
This was never about security. It was about who holds the key.
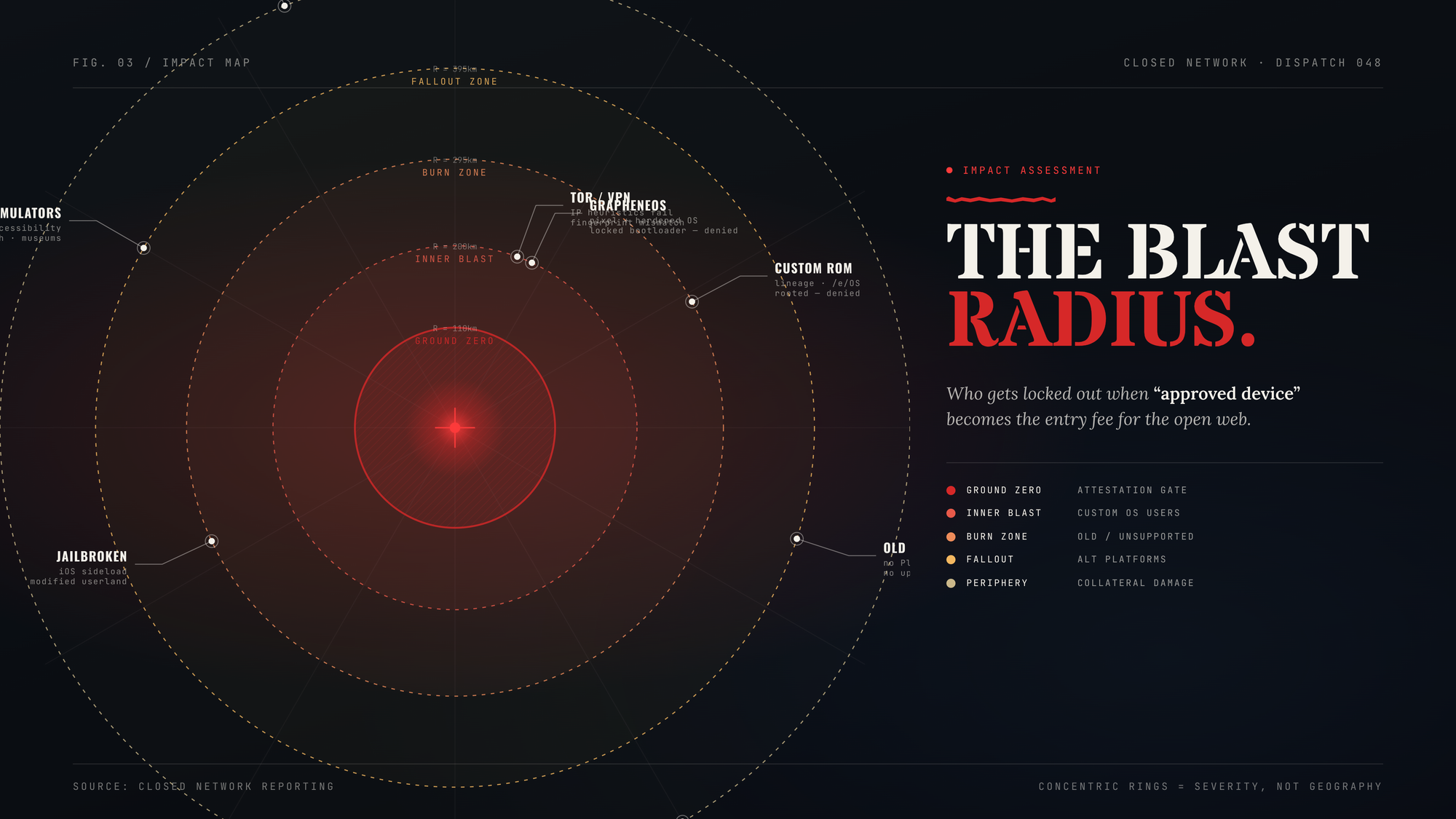
THE BLAST RADIUS
Picture, for a moment, the population of humans this policy quietly disqualifies from the open web.
GrapheneOS users. CalyxOS users. /e/OS, LineageOS, DivestOS, iodéOS users. Anyone running microG instead of Google Play Services. Anyone who unlocked their bootloader to escape carrier bloatware. Anyone holding an older Android device the OEM stopped certifying. Anyone running a desktop browser on Linux without an Android or iPhone in arm's reach. Anyone using a feature phone. Anyone who simply doesn't own a smartphone at all — a population that includes a non-trivial slice of the elderly, the rural poor, the homeless, and people in countries where smartphones are still a luxury.
And here's the kicker: the QR-code fallback exists today to soften the blow. The GrapheneOS team has been clear about where this is going. The mobile verification step is the on-ramp — the polite version. The next step is bringing the same hardware-attestation requirement directly to desktop browsers on Windows, macOS, and Linux. Once that lands, the QR code goes away. You either run a Google- or Apple-blessed stack end-to-end, or you don't pass.
Firefox on Linux, take a bow.
THE TROJAN HORSE THEY'RE RIDING IN ON
Hardware attestation is being sold to the public as the answer to bots, fraud, scraping, and AI-driven account abuse. And to be fair, it does work — a hardware-signed attestation is genuinely hard to forge at scale. Banks want it. Airlines want it. Government identity portals want it. Twitter wants it. Every company tired of paying for fraud-detection vendors wants it.
What gets quietly elided in the pitch is that the people deciding whether your device is "genuine" are the same two companies that already control 99% of the mobile operating system market, 100% of the trusted attestation infrastructure for those devices, and — starting in September with Android's developer-registration mandate — the right to decide which apps you're allowed to install in the first place.
Stack those policies on top of each other and the shape becomes hard to ignore. The OS verifies your age and broadcasts it to apps. The OS verifies which apps you're allowed to run. Now the OS verifies that you are allowed to use the open web. Three locks on the same door, all held by two companies headquartered fifty miles apart in California.
We covered this trajectory in Episode 53 — Locked Out. This week is what "locked out" looks like when it stops being a forecast and starts being a Tuesday.
WHAT YOU CAN ACTUALLY DO
Refuse the framing. Hardware attestation is not the same thing as security. It is one company's verdict about your device, dressed up as a security signal. A locked-down OS owned by Google is not safer than an open OS that publishes its source code and gets audited by adversaries; it is simply easier for Google to monetize. Every privacy-literate person you talk to this week needs to hear that distinction in plain language.
Pressure the sites that adopt it. The pain point in this whole scheme is the website. Google doesn't lose anything if your bank deploys reCAPTCHA Mobile Verification — the bank does, in lost customers and angry support tickets. If you get locked out, tell them, in writing, that you got locked out, and that you'll move your business if the policy stays. This is one of the rare moments where consumer email actually moves a needle.
Use alternatives where you can. Captcha, Cloudflare Turnstile, Friendly Captcha, and self-hosted options like Anubis and Cap solve the same bot problem without demanding hardware attestation. They aren't perfect — each has its own privacy trade-offs — but they don't require Google's blessing on your phone to use the web. If you run a site, switch.
Support the people fighting this in the standards bodies. GrapheneOS, the EFF, Mozilla, and the W3C TAG have all pushed back, hard, on remote attestation as a web requirement. Web Environment Integrity — Google's first attempt at this exact idea in 2023 — was killed by exactly that kind of pressure. The new flow is the second attempt, dressed up as a CAPTCHA. It can be killed too. But not by accident.
Keep running GrapheneOS anyway. The Hacker News commentator had a hundred clever workarounds within an hour — sand-boxed Play Services, attestation-spoofing modules, residential VPN exits, the works. Some of them work today. Most of them will be patched within a quarter. The technical arms race is real, and it matters, but it's not where this fight is won.
This fight is won in the framing. "Google decides which devices are allowed on the internet" is a sentence that, once spoken aloud to a normal person, immediately stops sounding like security and starts sounding like exactly what it is.
Say it out loud. Then say it again.
The open web didn't ask for permission to exist. It shouldn't have to ask for permission to continue.